CombiWAF
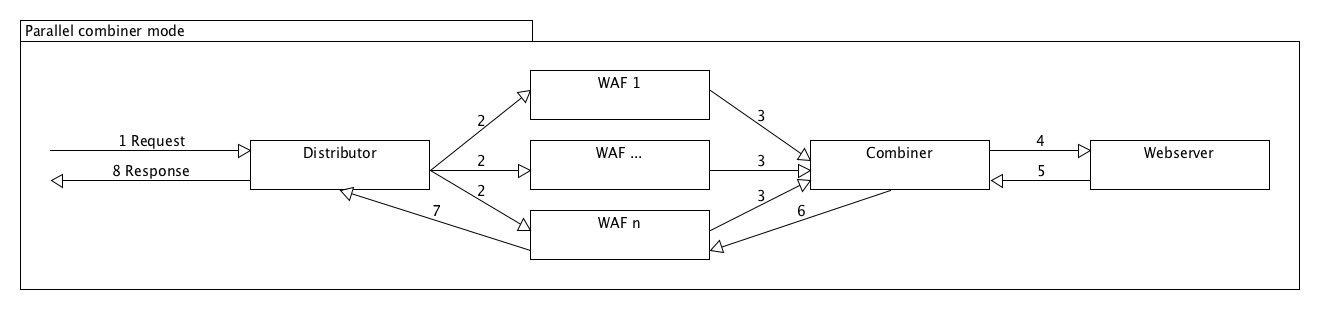
CombiWAF is a research application for the robust combination of web application firewalls (WAFs) . The main idea is that every WAF has weaknesses in different fields and by combining them, we can increase the security of the protected web server. The system consists of two parts:
- The distributor receives incoming HTTP(S) requests from external clients and forwards them to multiple WAFs in parallel. The first response from a WAF is then returned to the external client.
- The combiner receives requests from the WAFs which they cleared to reach the protected web server. Depending on the configuration, the combiner decides whether a cleared request should be forwarded to the web server. If yes, then it forwards it, takes the web server's response and send it back through one WAF.
The reference implementation is written in Go and runs on Linux/Unix and macOS systems.
Installation
git clone TODOorwget TODO- Make sure that the GOPATH environment variable is set properly (see https://github.com/golang/go/wiki/GOPATH )
- Change to the src directory of the downloaded code.
- Install dependencies with
go get. - Build the executable with
go build -o ../bin/combiwaf combiwaf.go.
Usage
To start the daemons, run combiwaf -distributor for the distributor or combiwaf -combiner
for the combiner. The PID will be written in the distributor.pid or combiner.pid file.
To kill a process, you can run e.g. kill `cat distributor.pid`.
Running the program without arguments shows the possible parameters with a
short explanation. You can run both components on different servers, of course.
Note: You can use both command line styles -param or --param.
General parameters
| Parameter | Default | Description |
-distributor |
Starts the distributor as a daemon. See distributor.log and distributor.pid for details. | |
-combiner |
Starts the combiner as a daemon. See combiner.log and combiner.pid for details. |
Parameters for the distributor
| Parameter | Default | Description |
-port |
8080 | External port to listen. This is the port for the incoming external requests. |
-timeout |
10000 | Timeout in milliseconds. Defines how long the distributor should wait for external connections before closing the connection without response. |
-waf-timeout |
10000 | WAF timeout in milliseconds. Defines how long the distributor should wait for a response from a WAF. |
-ssl |
false | Defines whether the distributor accepts SSL encrypted requests (HTTPS). |
-cert-file |
Certification file for the SSL connection. | |
-key-file |
Private key file for the SSL connection. | |
-wafs |
Comma-separated list of all WAFs with port like waf1.net:80,waf2.net:80,waf3.net:8080. Defines the WAFs to which an external request will be forwarded. |
Parameters for the combiner
| Parameter | Default | Description |
-port |
8080 | External port to listen. This is the port for the requests from the WAFs. |
-timeout |
10000 | Timeout in milliseconds. Defines how long the combiner should wait after receiving the first packet with a new UID before proceeding. |
-min-combiner-request |
2 | Minimum requests count for the combiner to proceed with a logic request. |
-web-server |
The web server address with port like example.com:80. Defines the protected web server to which\nthe request should be forwarded. | |
-wafs |
Comma-separated list of all WAFs with port like waf1.net:80,waf2.net:80,waf3.net:8080. Defines from which WAFs the combiner will receive requests. |
Example
-
Start the distributor (here as superuser because we want to bind to port 80)
combiwaf -distributor -port=80 -timeout=6000 -waf-timeout=5000 -wafs=waf1.internal:80,waf2.internal:80,waf3.internal:80
-
Start the combiner
combiwaf -combiner -port=8080 -timeout=2500 -min-combiner-requests=2 -web-server=webserver.local:80 -wafs=waf1.internal:80,waf2.internal:80,waf3.internal:80
-
Configure the used WAFs to forward the requests not to the web server, but to the combiner instead. (From the perspective of every WAF, the combiner is the web server.)
-
Configure the network so that only the distributor port is publicly available.
About
This project was developed side-by-side with the WAFuzz project for automatic, periodic evaluations of WAFs in different combination modes.